 As you may already know, I am a huge believer in two-factor authentication. You should keep in mind that two-factor authentication is not the absolute answer to Internet security problems. It is critical that you keep your computer patched with current antivirus software and that you browse and use email with care.
As you may already know, I am a huge believer in two-factor authentication. You should keep in mind that two-factor authentication is not the absolute answer to Internet security problems. It is critical that you keep your computer patched with current antivirus software and that you browse and use email with care.
I won’t get too much into the technology other than to say it involves using two of the three factors: a) something you know, b) something you have, and c) something you are. The majority of Internet two-factor authentication implementations use the first two factors, since determining something you are (such as a fingerprint or retinal image) involves considerably more logistics than is reasonable for a remote service. The something you know portion of the system is trivial and widely accepted as username/password combinations. Of course, password complexity is extremely important and will be the topic of a future post. That leaves us with something you have as the simplest and most common second factor.
It is worth noting that a second username/password combination can never be considered a second factor. Theoretically, an infinite number of passwords is still part of something you know. The primary reason that this is important is malware, particularly key-logging software. This is the reason I am disappointed in PayPal’s two-factor implementation, as described in my previous post on the subject. If you do implement two-factor authentication with PayPal, you should make sure you never bypass it or you risk exposing your account.
There are many unique and creative implementations of the second factor, and availability usually depends on the specific service you are accessing. For example, PayPal (I pick on PayPal because it’s widely known and accepted) allows the use of an SMS text message to deliver a one-time password (OTP), or the use of a key fob or security card that displays a new OTP every 30 seconds or with the press of a button.
 What I appreciate about PayPal is that they recognize the importance of two-factor authentication to the point that they heavily discount the price of the $48 Verisign security card to $5 (including delivery). See below for a way to save even more by getting the same security card functionality on your smart phone for free.
What I appreciate about PayPal is that they recognize the importance of two-factor authentication to the point that they heavily discount the price of the $48 Verisign security card to $5 (including delivery). See below for a way to save even more by getting the same security card functionality on your smart phone for free.
Other services, such as LogMeIn, use email instead of SMS to send you OTP’s.
One of the most unique second factor implementations I’ve encountered is called PhoneFactor. The premise behind PhoneFactor is that  entering a one-time password is time-consuming and inconvenient. How else can you prove you are in possession of a second factor without this inconvenience? By answering your phone of course! Once the service is installed and configured, logging into the appropriate service is as simple as entering your username/password combination and then answering your phone (cell or landline) and hitting the # key or optionally another PIN. The additional advantage of PhoneFactor is that by using your phone, you are using a separate out of band method of authenticating, which can be more secure. For example, a bank could use PhoneFactor to call you with the details of each transaction that you’d have to individually authorize. So unlike in-band Internet communications that can be easily intercepted and manipulated, it would be very difficult, if not impossible, for a hijacked session to intercept your telephone communications.
entering a one-time password is time-consuming and inconvenient. How else can you prove you are in possession of a second factor without this inconvenience? By answering your phone of course! Once the service is installed and configured, logging into the appropriate service is as simple as entering your username/password combination and then answering your phone (cell or landline) and hitting the # key or optionally another PIN. The additional advantage of PhoneFactor is that by using your phone, you are using a separate out of band method of authenticating, which can be more secure. For example, a bank could use PhoneFactor to call you with the details of each transaction that you’d have to individually authorize. So unlike in-band Internet communications that can be easily intercepted and manipulated, it would be very difficult, if not impossible, for a hijacked session to intercept your telephone communications.
The biggest challenge to wide-spread acceptance of two-factor authentication is standardization. Each service that you normally login to needs to have the second factor authentication component individually installed, configured and maintained. For example, despite the promise of improved Internet security for banking sites, only one, Associated Bank, is listed as a PhoneFactor client in their list of clients. This was a fairly recent announcement, however, so in time there may be many more options available. I recently found out PhoneFactor has created plugins for both WordPress (the software used to create this site) and LogMeIn, so there certainly is hope! I’ll likely be writing more about PhoneFactor in the future.
An interesting development on standardization is OpenID. OpenID works by having a supported web site contact your OpenID authority to confirm your identity. This is kind of a “put all your eggs in one basket” kind of scenario and there are some security concerns, the greatest is that it can be open to phishing attacks. This is where VeriSign’s Personal Identity Portal (PIP) and two factor authentication come into play.
My experience with VeriSign PIP started when I began using PassPack as my online password manager. While I’m really impressed with the service and continue to use it, one thing I don’t like about PassPack is that it doesn’t offer a two-factor authentication method (even the one-time passwords you can printout are only an alternative login method, not true two-factor). One thing it does allow, however, is the use of OpenID as an alternative login option. I italicized “alternative” because a user cannot setup OpenID as the only login method or even the default login method. It is provided more for convenience rather than security.
 When I investigated OpenID as an alternative login procedure, I searched on two-factor authentication and OpenID and landed on VeriSign’s PIP, which is still labeled “beta”. (I’m not sure if they’re hedging with the beta moniker, but it seems to be fully functional as far as I can tell.)
When I investigated OpenID as an alternative login procedure, I searched on two-factor authentication and OpenID and landed on VeriSign’s PIP, which is still labeled “beta”. (I’m not sure if they’re hedging with the beta moniker, but it seems to be fully functional as far as I can tell.)
One thing very cool that I discovered on the PIP site is that you can download a free copy of VIP Access for Mobile for your smart phone and, because it uses exactly the same technology, the software works as a valid security card for PayPal. To download the software directly to your phone, go to https://m.verisign.com from your phone’s browser.
Again, I recently found out that PhoneFactor also has an OpenID implementation that looks like a perfectly valid two-factor alternative to VeriSign. I’m becoming a fan!
So there you have it. To successfully and least expensively access both PayPal and OpenID with VeriSign’s PIP, use VIP Access for Mobile from VeriSign for free if you have a mobile phone, and use VeriSign’s security card from PayPal for $5 if you don’t. Either option is much less expensive than VeriSign’s identical (without the PayPal branding) $48 security card and even less expensive than VeriSign’s $6 delivery fee!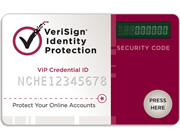 If you’re interested in in-house two-factor authentication at your company, or a solution for OpenID, WordPress or LogMeIn, I highly recommend that you check out PhoneFactor.
If you’re interested in in-house two-factor authentication at your company, or a solution for OpenID, WordPress or LogMeIn, I highly recommend that you check out PhoneFactor.

Good article. It’s a massive shame that UK mobile networks are charging too much so PhoneFactor don’t support mobiles in the UK 🙁 Seems like a very good idea.
Many of these 2 factor solutions allow a hacker access by just using your email address and password (which can both be keylogged) if the hacker claims that “I’ve lost my secure token”. I’ve documented the problem with VeriSign PIP here and suggested how it could be tackled to make a solution robust enough for online banking:
http://www.daveboden.com/Home/openidissues